Do you ever find yourself in need to browse the web from a network behind a firewall?
I’m curious if there’s a more direct route, but here’s what I did.
SSH Setup Reverse Tunnel
Borrowed from my post about setting this up for Remote Desktop.
On a LightSail instance on AWS (or your choice of linux servers)
sudo apt update
sudo apt install openssh-server
Edit the sshd_config
sudo vim /etc/ssh/sshd_config
At the bottom. Type “i” for insert then add the following lines
#Allow SSH Tunneling
GatewayPorts=clientspecified
To save: esc then “:wq” (command, wright, quit)
you can check that’s in there by running
cat /etc/ssh/sshd_config | Gate
response:
#GatewayPorts no
GatewayPorts=clientspecified
On your windows computer behind the firewall
Follow instructions from Microsoft to install OpenSSH:
https://learn.microsoft.com/en-us/windows-server/administration/openssh/openssh_install_firstuse?tabs=gui
Add to file ~/.ssh/config
#aws server
Host 123.123.123.123
User bitnami
IdentityFile ~/.ssh/id_rsa
IdentitiesOnly yes
ServerAliveInterval 60
ServerAliveCountMax 10
Adding ServerAliveInterval sets the number of seconds the client will wait before sending a keep connection alive
ServerAliveCountMax sets the number of times the client will try to keep connection alive.
you can also add this to the server as well.
vim etc/sshd/ssh_config
add
ClientAliveInterval 60
ClientAliveCountMax 10 #default is 3
Be sure to open up the correct port on your AWS firewall. I suggest restricting traffic on port 12345 only to the ip address of your client so you’re not opening up the port for nefarious actors.
In your terminal enter:
ssh 123.123.123.123 -2 -4 -T -N -C -R 0.0.0.0:12345:127.0.0.1:22
This creates an ssh tunnel, where a client can ssh into port 12345 on the AWS server which tunnels the traffic to your windows server behind the firewall.
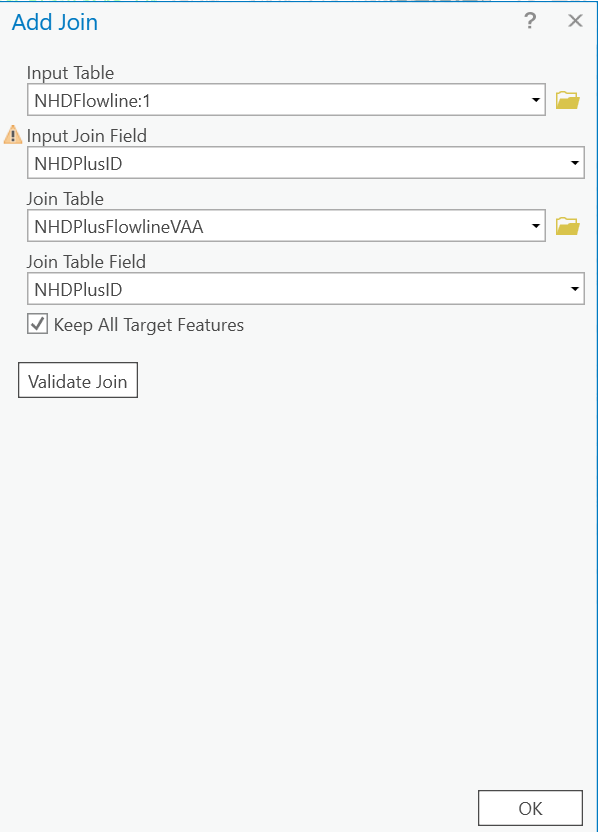
Tunnel HTTP through SSH Tunnel with PuTTY
On your client computer, install PuTTY with the msi
https://www.chiark.greenend.org.uk/~sgtatham/putty/latest.html
Use the PuTTYgen tool that’s installed to convert the private key to PuTTY’s .ppk format
Open PuTTY,
Host Name (of IP Address): 123.123.123.123 (ip of your aws server)
port: 12345
In the category field go to Connection -> SSH -> Tunnels
in source port: 8080
destination port: localhost:80
Select Dynamic
Click Add
Navigate back to Session
name the configuration, and save, then press open.
Because all traffic coming into 12345 on the aws server is routed to port 22 on the windows server, log in with your username and password for the windows machine. Once logged in, you’ll see the command prompt on your windows server.
Configure Proxy
Firefox is the easiest to set up. From options menu (top right) select Settings
At the very bottom of GENERAL, in the Network Settings section, select Settings
From the radio buttons, select Manural proxy configuration
in SOCKS Host: localhost
Port: 8080
Select Socks v5
Check the box next to Proxy DNS when using SOCKS V5
Test you setup
open google and search for “What is my ip”, The search result includes your IP address, it should be the IP of the WAN (Wide Area Network) of your windows server.
Troubleshoot
OpenSSH has a verbose mode. Add -v to your command for standard amount of verboseness. -vv will add even more info, -vvv will provide even more
Recap
The first tunnel is to forward all traffic from port 12345 on the AWS server to port 22 on the Windows Server
The Second tunnel forwards all traffic on port 80 (http) from your client computer (through the first tunnel), then requests the http traffic from the windows server.
Use SSH (without PuTTY)
In a terminal:
ssh -D 8080 -C -N [email protected] -p 12345
-D ::: Enables dynamic port forwarding, also known as a SOCKS proxy.
8080 is the binding port
-C ::: Enables compression
-N ::: Enables quiet mode
user ::: your windows server username
123.123.123.123 ::: Your AWS server
-p ::: Set ssh port
12345 ::: the port we want to connect to the AWS server so traffic is forwarded to the windows server
Activate Proxy on Mac
Settings -> Network -> (your network connection wifi/ethernet)
Details
From the details screen, select Proxies menu item.
activate SOCKS proxy.
Server: localhost
port: 8080